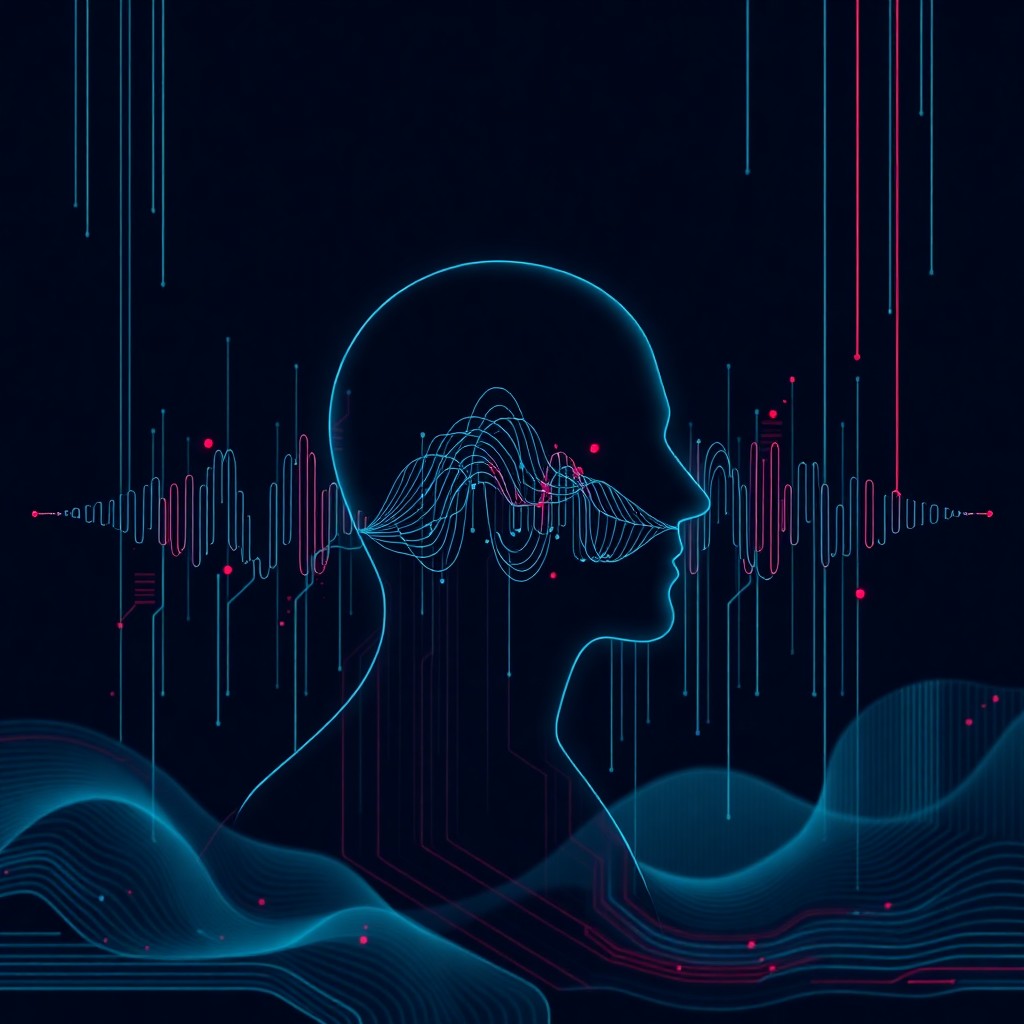
Artificial intelligence has reached a point where cloning human voices requires only seconds of audio samples. This technological breakthrough promises revolutionary benefits across entertainment, accessibility, and customer service industries. However, the same innovation has opened dangerous new pathways for cybercriminals to exploit unsuspecting victims through sophisticated social engineering attacks. As voice cloning technology becomes more accessible and affordable, understanding its mechanics and associated risks has become essential for individuals and organizations worldwide.
What Happened
Voice cloning technology has evolved dramatically over the past few years. What once required hours of recorded speech and specialized equipment can now be accomplished with three to ten seconds of audio and consumer-grade software. Major technology companies and startups have developed increasingly sophisticated algorithms capable of capturing not just the tone and pitch of a voice, but also subtle characteristics like breathing patterns, emotional inflections, and speaking rhythms. These systems use deep learning neural networks trained on vast datasets of human speech.
The proliferation of this technology has led to numerous security incidents worldwide. Cybercriminals have successfully used cloned voices to impersonate executives in business email compromise schemes, convince family members that loved ones are in distress during kidnapping scams, and bypass voice authentication systems protecting financial accounts. In one notable case, fraudsters used AI-generated voice cloning to impersonate a company CEO, resulting in a fraudulent wire transfer of hundreds of thousands of dollars. The technology has become so convincing that even security-conscious individuals struggle to distinguish authentic voices from synthetic reproductions.
How It Works
Voice cloning technology operates through sophisticated machine learning models called neural networks. These systems analyze audio samples to identify unique vocal characteristics including pitch, tone, accent, cadence, and pronunciation patterns. The process begins with training algorithms on massive datasets containing thousands of hours of human speech. Once trained, these models can generate new speech that mimics a target voice with remarkable accuracy.
Modern voice cloning typically follows a two-stage process. First, the system creates a digital representation of the target voice by analyzing provided audio samples. This representation captures the distinctive features that make each voice unique. Second, the system uses this representation to generate new speech from any text input, maintaining the characteristic sound of the original speaker. Advanced systems can even replicate emotional states, making the cloned voice sound happy, sad, angry, or concerned on demand.
The technology has become increasingly accessible through both legitimate commercial platforms and underground marketplaces. Some services offer voice cloning capabilities for as little as a few dollars, requiring minimal technical expertise to operate.
What You Should Do
Protecting yourself and your organization from voice cloning threats requires a multi-layered approach. Establish verbal authentication codes with family members and colleagues that can verify identity during unexpected calls requesting money or sensitive information. Never rely solely on voice recognition for high-stakes decisions, especially those involving financial transactions or data access.
Organizations should implement strict verification protocols for any requests involving fund transfers, password resets, or confidential information sharing. Use multiple communication channels to confirm unusual requests, and establish policies requiring written authorization for significant transactions. Consider deploying advanced authentication systems that analyze behavioral patterns beyond simple voice matching.
Limit the amount of voice data you share publicly through social media, podcasts, or video platforms. While complete avoidance is impractical, be mindful that any published audio can potentially be used for cloning purposes. Educate employees, family members, and team members about voice cloning risks and establish clear response protocols for suspicious communications.
As voice cloning technology continues advancing, vigilance and verification protocols become increasingly critical. The most effective defense combines technological safeguards with human awareness and established verification procedures. By understanding these risks and implementing protective measures, individuals and organizations can harness the benefits of AI innovation while defending against its malicious applications.
Stay protected with CyDhaal. Follow us at cydhaal.com for daily updates.